Azure Monitoring
HW sizing
Consider usage of our brand new full-stack infrastructure monitoring tool XorMon as LPAR2RRD replacement.
It brings a new level of infrastructure monitoring by relying on a modern technology stack.
In particular, reporting, exporting, alerting and presentation capabilities are unique on the market.
Follow installation procedure for your operating system platform
Implementation is agentless, all data is gathered from Azure Monitor API.
Create application under Azure Active Directory
- Log in to Microsoft Azure Portal
Switch to Azure Active Directory service
Note down your Tennant ID
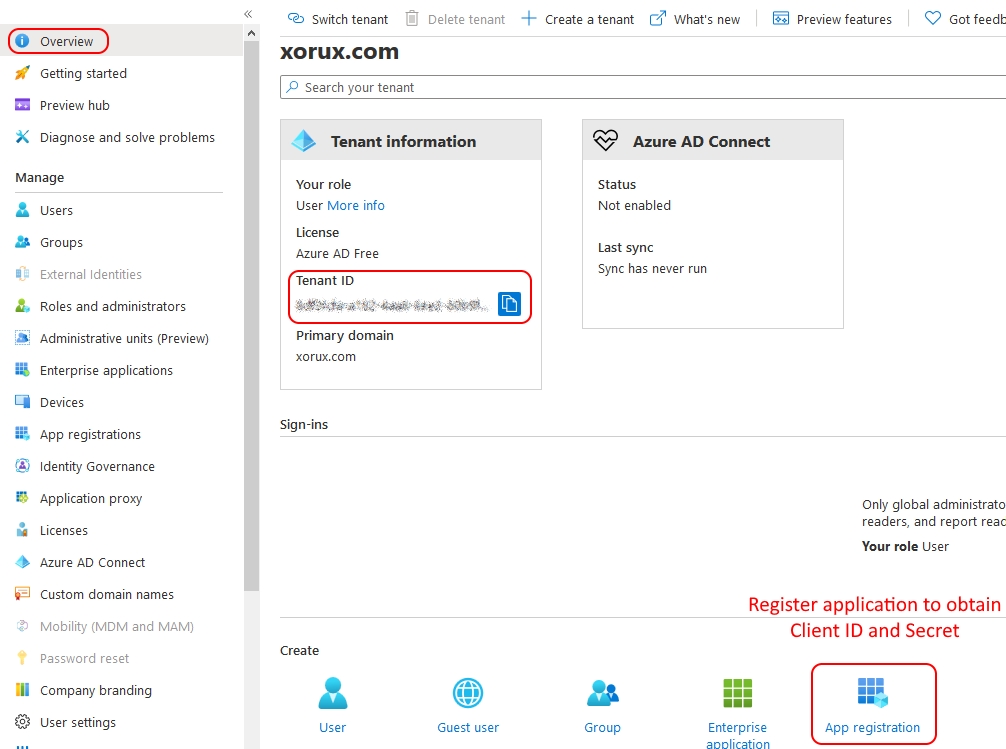
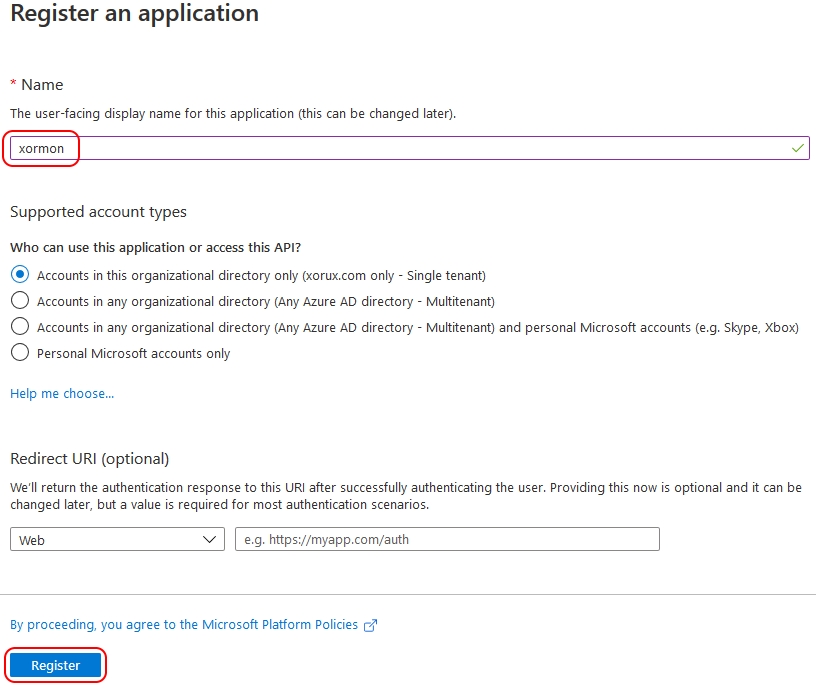
- Register a new application
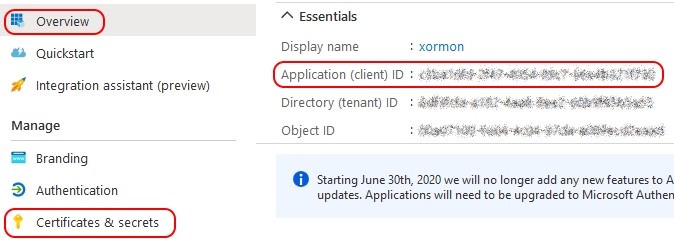
- Note down "Application (client) ID"
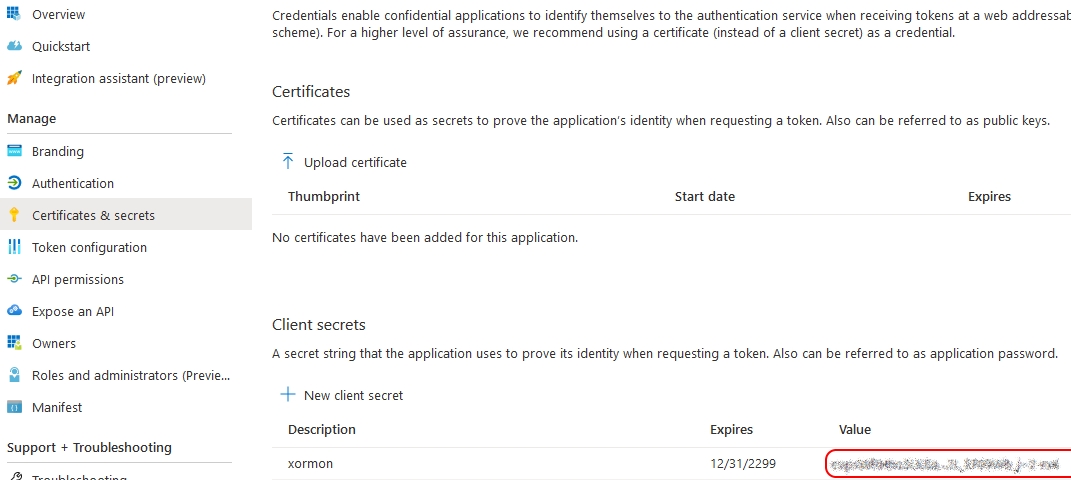
Go to "Certificates & secretes"
- Add "New client secret"
Note: you will have to repeat this process if you select expiration date
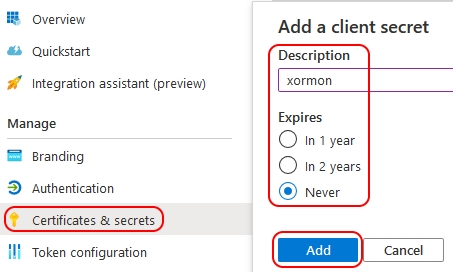
- Note down the Client secret
Add resources to application
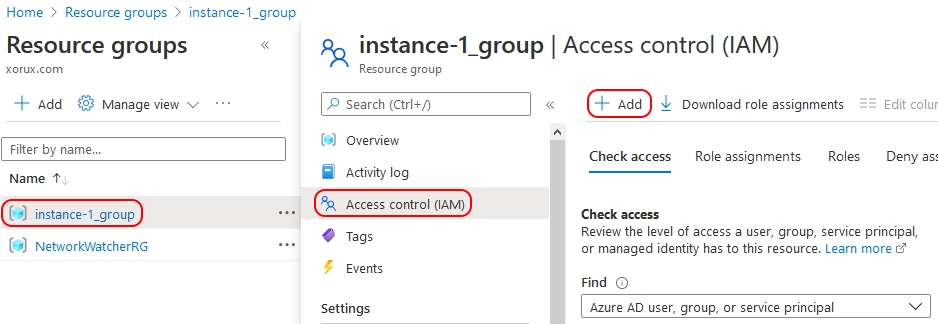
- Switch to Resource groups
Select your resource group
Note down resource group name and "Subscription ID" in the overview
Go to "Access control (IAM)"
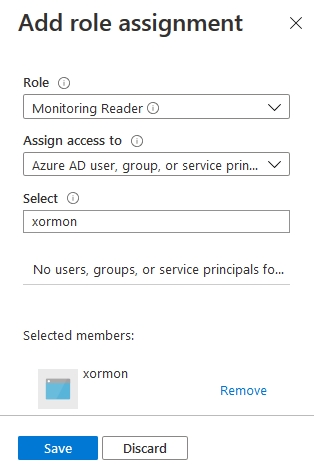
Add role to the resource group
- Select "Monitoring Reader" role for the newly registered application and save
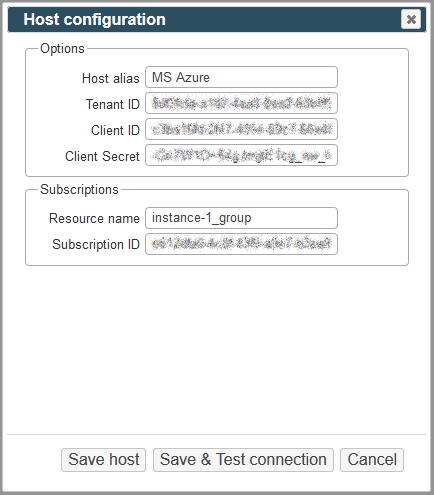
Configure Microsoft Azure in LPAR2RRD
-
LPAR2RRD UI ➡ Settings icon ➡ Azure ➡ New
Enter Host Alias, Tenant ID, Client ID, Client Secret, Resource name, Subscription ID
Save and run Connection Test
- Make sure cron job for Azure is in place (upgrade script might do it for you automatically)
Skip this step if you install the Virtual Appliance - it is already taken care of.Add following lines to crontab if necessary$ crontab -l | grep "load_azure.sh" $
$ crontab -e # Azure support 0,20,40 * * * * /home/lpar2rrd/lpar2rrd/load_azure.sh > /home/lpar2rrd/lpar2rrd/load_azure.out 2>&1
- Wait 30 minutes and then go to the web UI: http://<your web server>/lpar2rrd/
Use Ctrl-F5 to refresh the web browser cache.
Install LPAR2RRD server (all under lpar2rrd user)
-
Download the latest LPAR2RRD server
Upgrade your already running LPAR2RRD instance.
- Install it:
# su - lpar2rrd $ tar xvf lpar2rrd-7.XX.tar $ cd lpar2rrd-7.XX $ ./install.sh $ cd /home/lpar2rrd/lpar2rrd
- Make sure all Perl modules are in place
cd /home/lpar2rrd/lpar2rrd . etc/lpar2rrd.cfg; $PERL bin/perl_modules_check.pl
If there is missing "LWP::Protocol::https" then check this docu to fix it
- Enable Apache authorisation
umask 022 cd /home/lpar2rrd/lpar2rrd cp html/.htaccess www cp html/.htaccess lpar2rrd-cgi
- Schedule to run it from lpar2rrd crontab (it might already exist there)
Add if it does not exist as above$ crontab -l | grep load.sh $
$ crontab -e # LPAR2RRD UI 0,30 * * * * /home/lpar2rrd/lpar2rrd/load.sh > /home/lpar2rrd/lpar2rrd/load.out 2>&1
Assure there is just one such entry in crontab.
- You might need to add lpar2rrd user into /etc/cron.allow (Linux) or /var/adm/cron/cron.allow (AIX) if 'crontab -e' command fails
Allow it for lpar2rrd user as root user.# echo "lpar2rrd" >> /etc/cron.allow
- Make sure you have a cron job for Azure is in place (upgrade script might do it automatically)
Skip it on the Virtual Appliance, it is already there.
Add it if it does not exist like above
$ crontab -l | grep "load_azure.sh" $
$ crontab -e # Azure support 0,20,40 * * * * /home/lpar2rrd/lpar2rrd/load_azure.sh > /home/lpar2rrd/lpar2rrd/load_azure.out 2>&1
-
Initial start from cmd line:
$ cd /home/lpar2rrd/lpar2rrd $ ./load.sh
- Go to the web UI: http://<your web server>/lpar2rrd/
Use Ctrl-F5 to refresh the web browser cache.
Troubleshooting
-
If you have any problems with the UI then check:
(note that the path to Apache logs might be different, search apache logs in /var)tail /var/log/httpd/error_log # Apache error log tail /var/log/httpd/access_log # Apache access log tail /var/tmp/lpar2rrd-realt-error.log # STOR2RRD CGI-BIN log tail /var/tmp/systemd-private*/tmp/lpar2rrd-realt-error.log # STOR2RRD CGI-BIN log when Linux has enabled private temp
- Test of CGI-BIN setup
umask 022 cd /home/lpar2rrd/lpar2rrd/ cp bin/test-healthcheck-cgi.sh lpar2rrd-cgi/
go to the web browser: http://<your web server>/lpar2rrd/test.html
You should see your Apache, LPAR2RRD, and Operating System variables, if not, then check Apache logs for connected errors